
HIPAA Compliant Live Chat: How to Outsource Safely
Live chat in healthcare is not like live chat anywhere else. A customer service agent asking "can I get your order number?" is a different conversation than one asking "can I confirm your date of birth and insurance ID?" The first is routine. The second triggers federal law.
HIPAA compliance in live chat outsourcing is not primarily a software question. Encryption matters, yes. But the bigger risk is operational, who is accessing patient data, how they were trained, what happens when something goes wrong, and whether your vendor ever signed a Business Associate Agreement.
Healthcare organizations that outsource live chat and get this wrong face penalties that start at $100 per violation and reach $2.2 million per violation category per year. The reputational damage goes further than the fines.
This article covers what HIPAA requires from a live chat operation, where outsourcing arrangements typically fail, and what a genuinely compliant healthcare BPO partner looks like.
Key takeaways
- Any live chat session where protected health information (PHI) is accessed, discussed, or transmitted is subject to HIPAA's Privacy and Security Rules.
- A Business Associate Agreement (BAA) is legally required before sharing PHI with any outsourced vendor. No BAA means no compliant outsourcing.
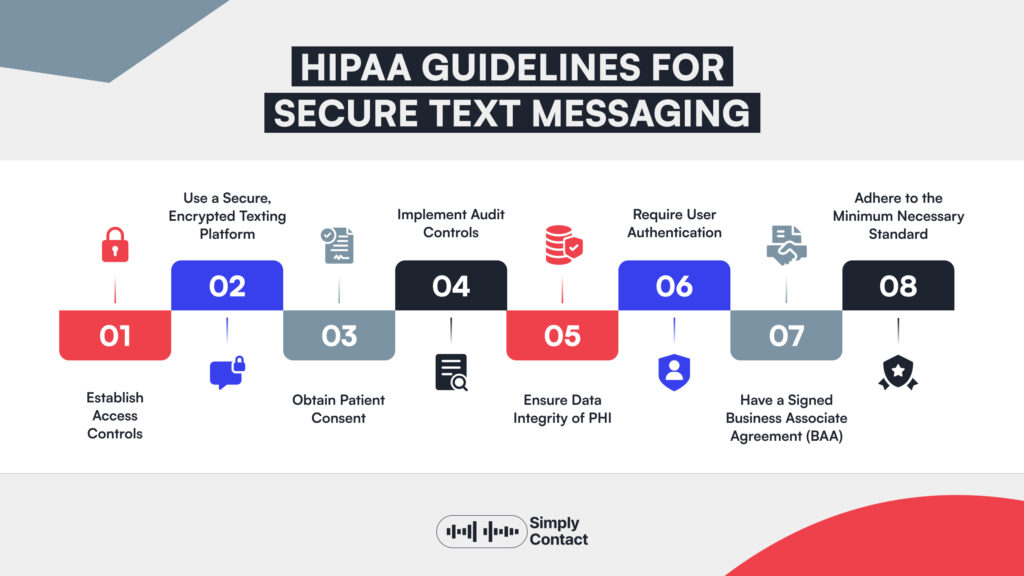
- Compliance is an operational question as much as a technical one: agent training, access controls, and incident response matter as much as encryption.
- HIPAA violations carry penalties up to $2.2 million per violation category per year, and the OCR actively investigates contact center breaches.
- Choosing a BPO partner means vetting their entire compliance infrastructure, not just their software stack.
What HIPAA means for live chat in a healthcare context
HIPAA's Privacy Rule governs how protected health information can be used and disclosed. Its Security Rule governs how electronic PHI (ePHI) must be protected. Both apply the moment a live chat session touches patient data and in healthcare support, that happens constantly.
- PHI in a chat session includes their name combined with a date of service, their insurance ID, their appointment history, any billing information tied to a medical record. If an agent confirms an appointment, answers a billing question, or helps a patient reset access to their health portal.
- The BAA requirement is the most commonly misunderstood part of healthcare contact center outsourcing. HIPAA defines any vendor who creates, receives, maintains, or transmits PHI on behalf of a covered entity as a Business Associate. That definition covers live chat outsourcing providers directly. The BAA establishes what the Business Associate can do with PHI, how they must protect it, and what they must do if a breach occurs.
One important framing note: HIPAA compliance in live chat is not about the chat software alone. A HIPAA-compliant chat platform with inadequately trained agents, loose access controls, or no breach response protocol is not a compliant operation. The Privacy and Security Rules apply to the full system: people, process, and technology together.
Risks of outsourcing healthcare chat without compliance controls
Healthcare organizations that outsource live chat without adequate compliance controls expose themselves to a specific set of risks. These are not hypothetical, the Office for Civil Rights (OCR) has levied multi-million dollar settlements against healthcare organizations for exactly these failures.
- Data breach through unencrypted channels. Chat sessions that transmit ePHI over unencrypted connections are a direct HIPAA violation under the Security Rule. This includes chat logs stored without encryption at rest, and transcripts emailed or exported in plain text. A breach involving 500 or more patients triggers mandatory OCR reporting and public listing on HHS's "Wall of Shame."
- BAA gaps with subcontractors. Many BPO providers use subcontractors for overnight shifts, overflow volume, language support. If the primary vendor has a BAA with you but their subcontractors do not have BAAs with them, the chain of accountability is broken. PHI can reach parties with no legal obligation to protect it.
- Agent training failures. HIPAA requires that workforce members with access to PHI are trained. That obligation doesn't disappear when you outsource. If agents handling your healthcare chat haven't received documented HIPAA training, your organization shares the liability for what they do with patient data. A single agent who emails a chat transcript to the wrong address, or discusses a patient's information in an unsecured environment, can trigger a reportable breach.
- No audit trail. The Security Rule requires covered entities and their Business Associates to maintain audit controls: records of who accessed ePHI and when. Live chat operations without logging and access tracking cannot demonstrate compliance if an incident occurs.
- Inadequate incident response. HIPAA's Breach Notification Rule requires covered entities to notify affected individuals within 60 days of discovering a breach, and to notify HHS. If your outsourced live chat vendor has no documented incident response protocol, you may not discover a breach until it's too late to comply with the notification timeline.
HIPAA violation penalties are tiered by culpability. Violations due to reasonable cause with no willful neglect start at $1,000. Violations due to willful neglect that are not corrected reach $50,000 per violation, with an annual cap of $2.2 million per violation category. Multiple categories can apply simultaneously.
What to require from an outsourced live chat partner
When evaluating a healthcare customer service outsourcing partner for HIPAA compliant live chat, the following requirements are non-negotiable.
| Requirement | What to Ask For | Key Details |
| Business Associate Agreement | Signed BAA before any PHI is shared | Must cover all subcontractors, not just the primary vendor |
| End-to-end encryption | Encryption specs for transit and storage | TLS 1.2+ in transit; encrypted transcripts, logs, backups and exports. Ask about access and disposal |
| Documented HIPAA training | Training records per agent | Must include date, content, agent name. Ask about re-certification frequency and scenario-based testing |
| Role-based access controls | Access policy documentation | Minimum necessary access only; must be auditable and immediately revocable on departure |
| Audit logs & monitoring | Sample access log format | Logs must be tamper-evident and retained for a minimum of 6 years |
| Incident response protocol | Written breach response procedure | Must cover detection, notification timeline, and how your compliance team is reached across time zones |
| Physical & environmental controls | Remote work and device policy | Screen lock, clean desk requirements; company-managed devices with endpoint security for remote agents |
A vendor who cannot clearly answer questions about any of these areas is not ready for HIPAA compliant live chat outsourcing, regardless of what their sales materials say.
How Simply Contact handles HIPAA-compliant healthcare chat
Simply Contact holds ISO 27001 certification for information security management, ISO 27701 certification for privacy information management, GDPR compliance, and HIPAA compliance PCI DSS for security of card information. These are independently audited certifications that define how patient data is handled at the process level, not just the technology level.
Henri Demianovich, Information Security Lead at Simply Contact adds: “Security is not a state to be achieved, but rather a systematic, documented and tested process that is proven to be effective. At Simply Contact, we have developed an information security management system that covers all aspects: technical, organizational, physical and, most importantly, our people. We continuously train our agents and management. Our employees incorporate information security into their daily work.”
For healthcare and health-adjacent clients, the operational approach is built around three principles:
- Controlled data access. Agents are given access only to the systems and data required for their specific role. Access is logged, monitored, and reviewed. When an agent's assignment changes or ends, access is revoked immediately. This role-based model is the practical implementation of HIPAA's Minimum Necessary standard.
- Structured agent training. HIPAA training is mandatory before any agent handles healthcare-related contacts. Training covers the specific obligations under the Privacy and Security Rules, common scenarios where PHI is at risk, and breach reporting procedures. Re-certification is scheduled, not optional. Simply Contact's AI call simulation infrastructure, which reduced agent onboarding time by 30% across programs, can deliver HIPAA scenario training at scale across multiple languages, meaning compliance training doesn't create a bottleneck for teams that need to ramp quickly.
- Security infrastructure. ISO 27001 certification requires a formal Information Security Management System: documented policies, risk assessments, access controls, and regular audits. ISO 27701 extends this to privacy management specifically. Together they provide a compliance foundation that covers the Security Rule's administrative, physical, and technical safeguard requirements.
For example, for HATS Group, a UK-based provider of non-emergency patient transport services, we have provided the client’s contact center team, managing the full customer support journey across both inbound and outbound channels.
The Simple Contact team managed to build a system that protects public resources while treating every caller with dignity. Every interaction was guided by empathy, clarity, and accountability, proving that efficient public service can still feel deeply human. We supported 16 service languages, 6,000 monthly calls, and a 93.9% quality score, to deliver trust at scale.
For healthcare organizations evaluating live chat outsourcing or call center support outsourcing, the compliance infrastructure is already built. The BAA question has a ready answer.
Common mistakes when outsourcing live chat in healthcare
The same mistakes come up repeatedly in healthcare contact center outsourcing arrangements that later result in HIPAA violations.
- Selecting software without vetting the people operating it. The most common mistake. A healthcare organization demos a HIPAA-compliant chat platform, signs a BAA with the software vendor, and assumes compliance is handled. The platform is compliant. The BPO operating it may not be. The agents accessing PHI through that platform need their own training, their own access controls, their own audit trail. The platform vendor and the outsourcing vendor are different Business Associates with different obligations.
- Treating the BAA as a one-time paperwork step. BAAs need to reflect the actual scope of the engagement. If the outsourcing arrangement expands (more agents, new subcontractors, additional channels) the BAA may need to be updated. Organizations that sign a BAA at the start and never review it can find themselves operating outside its scope years later.
- Skipping ongoing compliance audits. HIPAA compliance in live chat outsourcing is not a setup task. The OCR expects covered entities to conduct periodic assessments of their Business Associates' compliance. Annual reviews, access log audits, and periodic re-testing of incident response procedures are part of a functioning compliance program — not extras.
- Assuming that offshore or nearshore teams can't be HIPAA compliant. HIPAA applies to covered entities and their Business Associates regardless of where agents are located. Geography is not a compliance barrier. What matters is whether the vendor's infrastructure, training, and controls meet the standard. A well-run contact center in any location can operate a HIPAA compliant live chat program. A poorly run one in any location cannot.
- No channel-specific policies. Organizations with HIPAA policies for phone and in-person interactions sometimes fail to extend those policies to live chat and other digital channels. Chat transcripts are ePHI. Screenshots of chat sessions are ePHI. Policies need to cover the channel explicitly, not assume existing phone policies transfer automatically.
For a broader look at how customer service in healthcare intersects with compliance obligations, the structural requirements are similar across channels, what changes is the specific technical safeguard for each medium.
HIPAA compliant live chat outsourcing is an operational question
Software that encrypts data is a necessary condition for HIPAA compliant live chat. The regulation covers people and processes as fully as it covers technology, which is why organizations that evaluate BPO partners purely on their tech stack keep running into problems.
The right questions to ask are: show me your BAA template, walk me through your agent training program, explain your breach response timeline, and tell me how you handle access controls for remote agents.
A partner who can answer those questions specifically, with documentation, is a partner worth having a compliance conversation with. One who deflects to "we use HIPAA-compliant software" is not.
Talk to our team about what HIPAA compliant live chat outsourcing looks like for your organization.
At Simply Contact, we specialize in creating personalized customer support solutions that drive business growth and customer satisfaction. Let us help you elevate your customer experience and stand out from the competition.



